Recently we have received many inquiries on whether Radiator AAA would be a good solution for replacing Juniper’s Steel-Belted RADIUS. As the aforementioned SBR has reached End of Engineering date in February, its support ending in September and with seemingly no alternative from the OEM, many operators are looking to replace their existing SBR setups with alternative established robust AAA solution. If you are among these companies, Radiator AAA is the solution for you.
Why choose Radiator AAA?
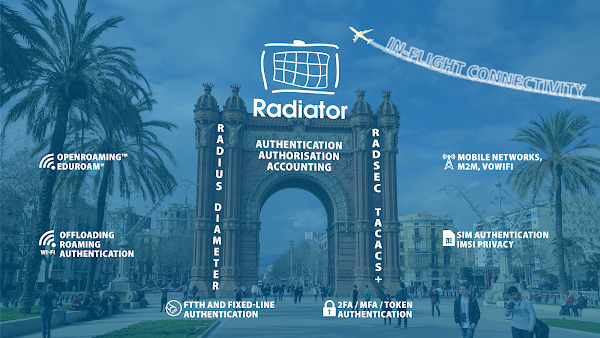
Known for its reliability and flexibility, Radiator AAA has been in the market for decades. Radiator is an actively developed and support AAA server with RADIUS and TACACS+ functionalities. With modules, Radiator AAA can also be complemented with Diameter relay, SIM-based authentication and other mobile network functionalities.
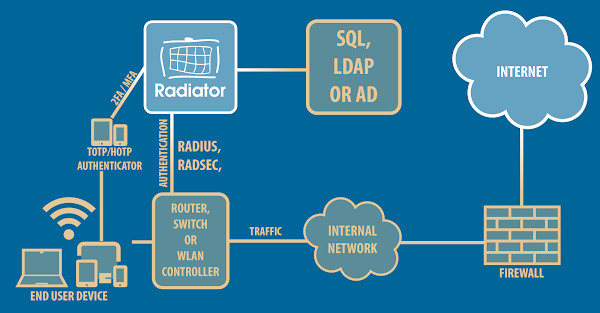
Like SBR, Radiator AAA Server offers support for both Linux, Windows and Solaris installations with various different operating systems (See our Supported Platforms for more information. Radiator has extensive support for different databases and authentication backends (SQL-based, LDAP, AD etc.) as well as support for MFA solutions with TOTP capable authenticators and tokens (Google and MS authenticator, Yubikey, DIGIPASS etc.)
The Radiator technical team consists of experts with vast experience in migration from other AAA solutions. We offer migration support and configuration assistance so you do not need to worry about meeting project schedule before SBR EoSL. Radiator can integrate with existing database and in nearly all cases no changes to schema are needed.
Like Steel-Belted RADIUS, Radiator AAA has multi-vendor support and can be installed flexibly on different platforms on physical or virtual machines. With Radiator, you can compile your AAA use cases under one product: RADIUS, Diameter, TACACS+, SIGTRAN, you name it, we have it!
Want to know more?
For any questions or other inquiries about Radiator as SBR replacement, please contact sales@radiatorsoftware.com